Client Credentials Grant Type in OAuth 2.0
The Client Credentials Grant Type is specifically designed for applications that need to access resources not associated with a particular user. In this scenario, the client acts as the resource owner. This grant type is most appropriate for back-end systems where the application interacts with a service without any user context.
How It Works
Requesting the Token:
- The client sends a request to the authorization server. This request usually includes the client's
client_idandclient_secretto authenticate itself.
Token Response:
- After successfully authenticating the client, the authorization server issues an access token. The client can then use this token to request resources from the resource server.
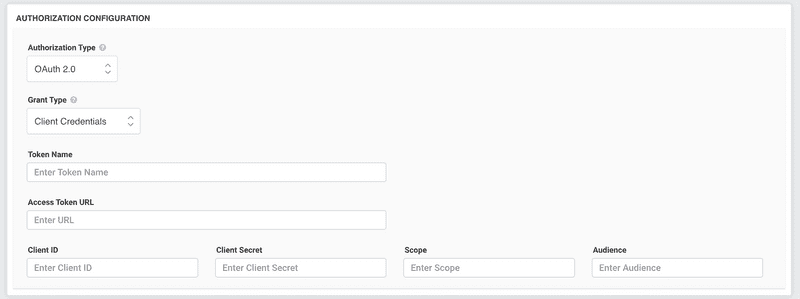
Configuring the Client Credentials Grant
Register Your Application:
- Begin by registering your application with the OAuth 2.0 provider. After registration, you should receive a
client_idandclient_secret.
Token Request:
- Your application needs to send a POST request to the token endpoint of the authorization server. This request should include the
grant_typeparameter set to "client_credentials", and theclient_idandclient_secret. It's crucial to send this request securely, using HTTPS.
Handle the Token Response:
- The authorization server will respond with an access token once it verifies your application. Handle this token securely within your application.
Use the Token:
- With the access token in hand, your application can send authorized requests to the resource server to access the allowed resources.
Points to Consider
No User Interaction: This grant type does not involve end-user authentication, making it suitable for server-to-server interactions.
Security: Given that application credentials (
client_idandclient_secret) are essential for obtaining the token, it's imperative to keep them secure. Any security lapse could lead to unauthorized access.Limited Scope: Tokens acquired via this flow should be limited in their scope, granting only the permissions necessary for the application to function.
Conclusion
The Client Credentials Grant Type provides an efficient way for applications to communicate with a service without user intervention. It's the preferred method for situations where an application needs to operate on its behalf, not on behalf of a user. However, developers need to be cautious and ensure the security of the application's credentials to prevent potential security risks.