How to Secure Your API Integrations with Best Practices
This template provides best practices for securing API integrations, focusing on strategies that enhance both functionality and security in API implementations. It emphasizes the importance of reliable monitoring in ensuring optimal performance.
What is How to Secure Your API Integrations with Best Practices?
This template outlines essential strategies for securing API integrations, providing guidelines that help developers and organizations implement robust security measures. By adhering to these best practices, you can effectively protect sensitive data and ensure the integrity of your API communications.
API security is critical because APIs often serve as gateways to backend systems, making them potential targets for malicious attacks. Implementing best practices in API security can significantly reduce vulnerabilities. Let's examine key elements:
Authentication and Authorization
Ensuring that only authorized users can access your APIs is paramount. Implement robust authentication mechanisms such as OAuth and API keys, and enforce strict authorization checks to limit access to sensitive functions.
Data Encryption
Encrypting data in transit and at rest protects sensitive information from eavesdropping and unauthorized access. Use HTTPS for secure communication and consider encrypting payloads to bolster security.
Input Validation
Always validate input data to prevent injection attacks and ensure that your APIs only process expected data formats. This practice helps safeguard against common vulnerabilities.
Rate Limiting and Throttling
Implement rate limiting to control the number of requests a user can make within a certain timeframe. This helps prevent abuse and ensures fair usage of your APIs.
Monitoring and Logging
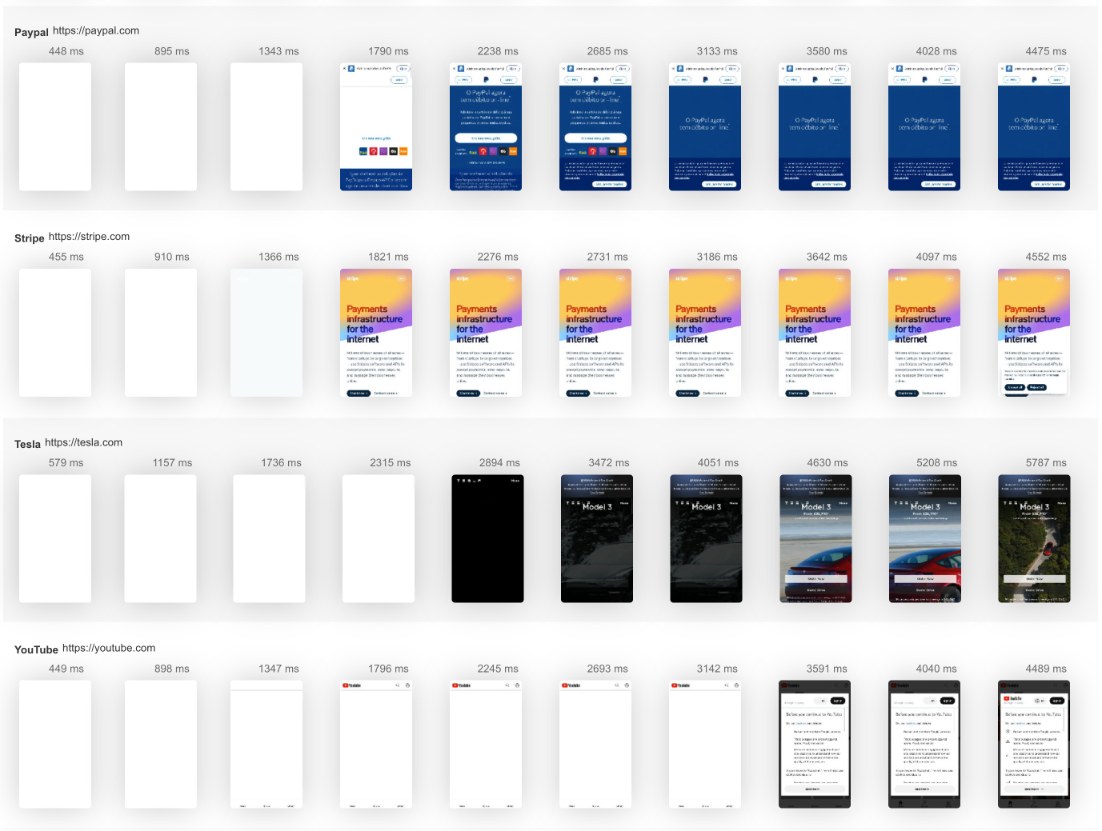
Regularly monitor API usage and maintain detailed logs of requests and responses. These logs are invaluable for detecting unusual activity and troubleshooting issues.
How is this related to API Monitoring Tool/Service?
Utilizing an API monitoring service like LoadFocus can significantly enhance your security strategy. API monitoring tools allow you to continuously assess the performance and availability of your APIs while providing insights into any security vulnerabilities or anomalies. With real-time alerts, you can respond swiftly to potential threats.
Moreover, monitoring ensures that your APIs are functioning as intended, which is crucial for maintaining user trust and operational integrity. By integrating security best practices into your API monitoring strategy, you can create a comprehensive approach that safeguards your systems while optimizing performance.
FAQ on How to Secure Your API Integrations with Best Practices
What is API security and why is it important?
API security involves protecting APIs from unauthorized access and threats, ensuring that sensitive data is kept safe and that APIs function as intended.
What are common API security threats?
Common threats include injection attacks, data breaches, denial of service attacks, and unauthorized access, which can compromise sensitive information.
How can I monitor my API for security vulnerabilities?
Utilize API monitoring tools that provide real-time insights and alerts for unusual activity, helping you detect and respond to potential security issues promptly.
What role does encryption play in API security?
Encryption protects sensitive data in transit and at rest, making it difficult for unauthorized parties to access or tamper with the information.
What are some best practices for API authentication?
Implement robust authentication methods such as OAuth, API keys, and JWTs to ensure that only authorized users have access to your APIs.
How fast is your website?
Elevate its speed and SEO seamlessly with our Free Speed Test.You deserve better testing services
AI-powered load test analysis included on all paid plans. Load test websites, measure page speed, and monitor APIs with AI insights that explain your results in plain English.Start for free→